Understand your privacy exposure before it is tested under pressure.
See where you stand — then close gaps, build defensible evidence, and move into a structured workspace when you are ready.
See where you're exposed
Visibility before regulators ask.
Systems, vendors, governance.
Know exactly what to fix
Clear gaps and priorities.
Framework-aligned, actionable.
Evidence when you need it
Defensible proof in one place.
Audit-ready, on demand.
Need a fast read? Run a quick exposure check · View Pricing
Keep clarity high and exposure low.
CyberCorrect is designed so organizations can start quickly without forcing sensitive privacy work into a slow, consultant-heavy process.
Fast entry
Start with standalone checks when the immediate need is clarity, not full deployment.
Private workspace option
Move into a fuller privacy execution environment when you need structured records, analysis, and evidence.
Defensible outputs
Focus on what can be explained under scrutiny: exposure, controls, documentation, and next actions.
Common exposure patterns
Where your organization is exposed today
These gaps become visible when a request, complaint, or audit forces scrutiny.
No clear view of data across systems and vendors
Hidden risk across your environment before it's challenged
Third-party access without mapped controls
Risk inherited from vendors you don't fully see
Rights requests without defined workflows
Triggered by real user requests (access, deletion, opt-out)
Unclear applicable obligations
Gaps you can't confidently justify
Maryland MODPA is about to change what “good enough” privacy looks like.
Maryland's Online Data Privacy Act (MODPA) applies when controllers meet statewide volume or revenue thresholds—not by default for every business.
- In scope or not depends on data scale, revenue mix, and how you process Maryland residents' personal data—not branding or intent.
- Risk shows up in the gap between “we think we're fine” and defensible evidence.
Do you already know—with specifics—which side of the thresholds you are on?
Also: MODPA Review™ BusinessMODPA Review™ School. Free browser-based tools · No account required for diagnostics.
Primary threshold signal
Controllers that process personal data of 35,000+ Maryland consumers in a calendar year generally sit in scope.
Secondary threshold signal
10,000+ Maryland consumers when more than 20% of gross revenue comes from the sale of personal data.
What businesses need now
A clear applicability position, documented inventory and purposes, and workflows for notices and consumer rights—so enforcement isn't the first time you find gaps.
Turn privacy uncertainty into a clear action plan
Typical blind spots on the left — a grounded operating path on the right. Click any region to open the matching review or resource.
Start with a privacy review — open the workspace when you're ready to operationalize.
Prefer a walkthrough? How it works
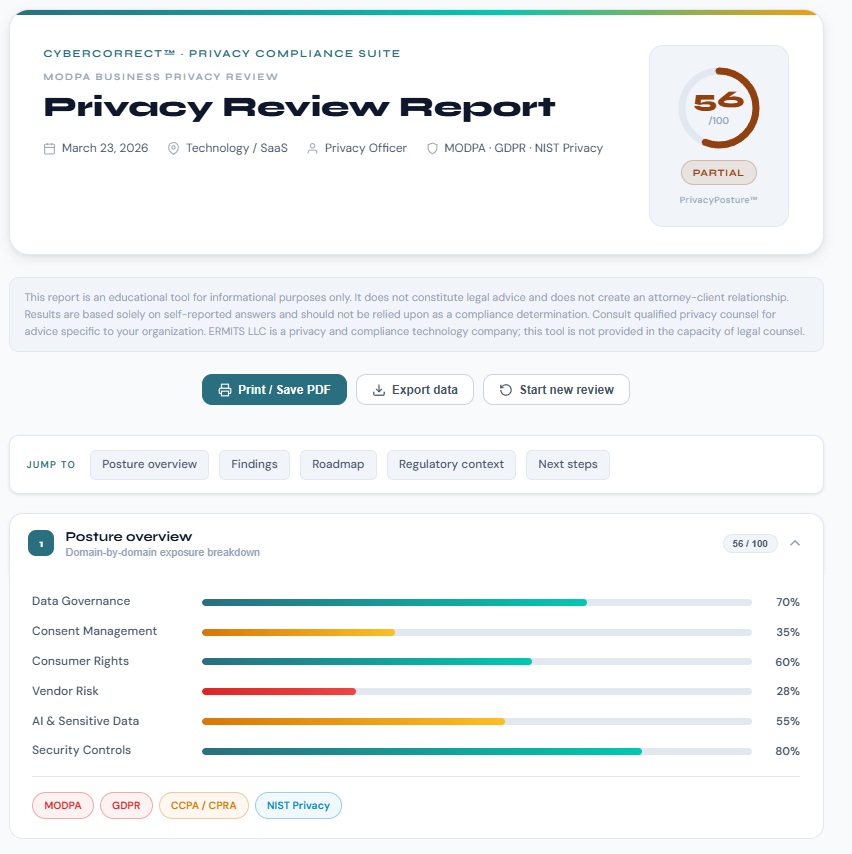
From exposure to defensible decisions
Identify your gaps and risk, understand what to fix, and build evidence aligned with real privacy obligations.
Exposure discovery
See where your organization stands across data flows, vendors, and obligations — before an audit or request forces visibility.
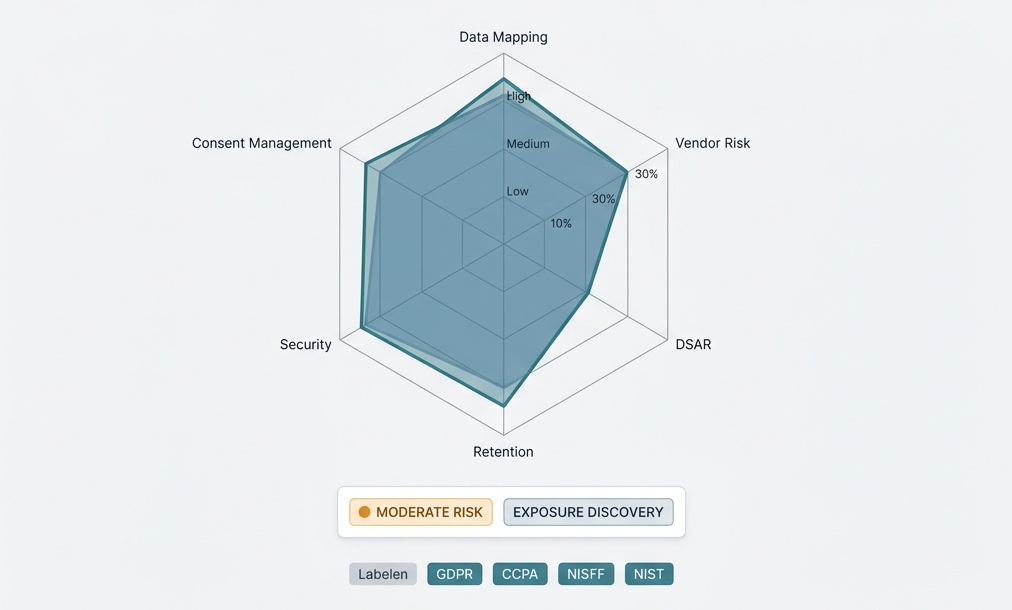
What to fix first
Understand what gaps matter most and what actions reduce your risk — with clear priorities, not checklists.
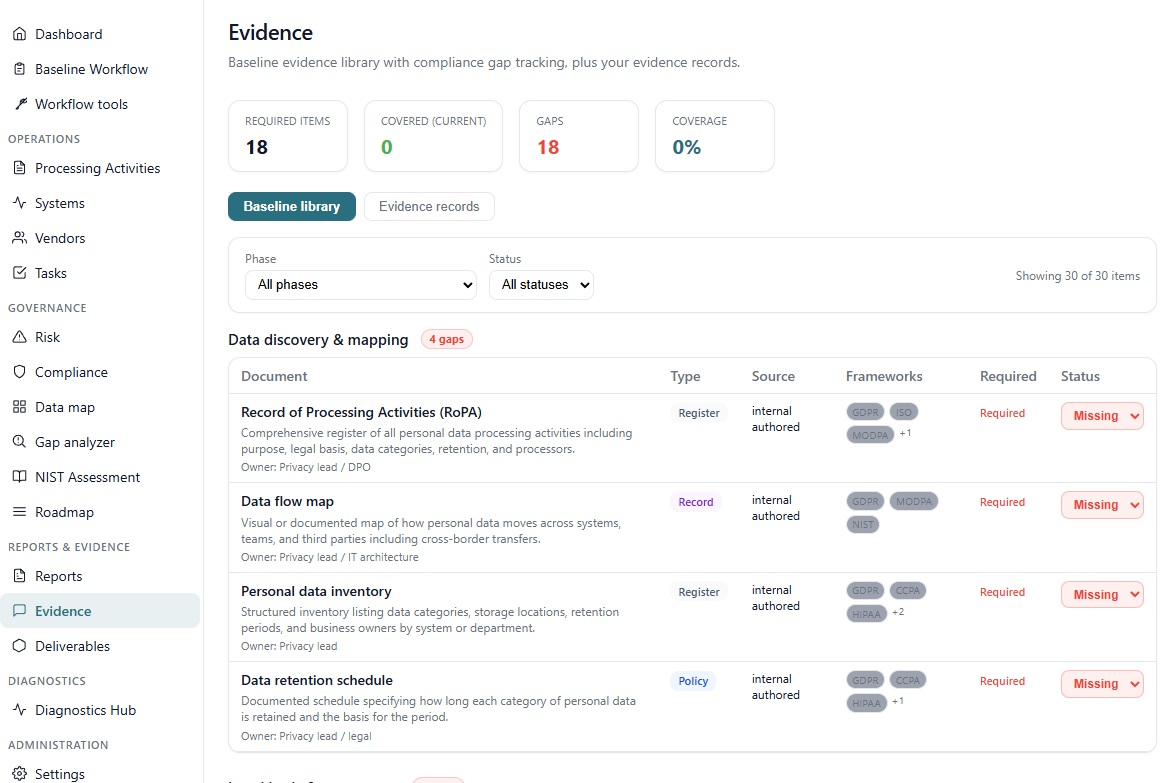
Audit-ready evidence
Build structured records, assessments, and evidence so you can respond confidently to regulators, customers, and internal stakeholders.
Move from visibility to prioritized fixes and audit-ready evidence.
Prefer a walkthrough? How it works
What the workspace delivers.
From inventory to audit-ready outputs: mapping, registers, impact assessment support, obligation coverage, evidence, and reporting.
Data mapping
Systems, vendors, and personal data flows in one structured view so processing is visible and maintainable.
RoPA — Record of Processing Activities
Registers linked to your inventory—aligned with how data is actually collected, used, and shared.
DPIA — Data Protection Impact Assessment
Workflow support to identify high-risk processing, document analysis, and follow-up actions.
Requirements mapping
Map obligations and controls across major frameworks so gaps, overlaps, and priorities stay tied to real processing.
Evidence
Structured artifacts and an audit trail you can retrieve when legal, security, or regulators ask for proof—not ad hoc screenshots.
Reporting
Summaries and exports for leadership, customers, and oversight bodies—consistent with the records you keep in the workspace.
Put mapping, registers, and evidence on one spine—not scattered files and decks.
Privacy-First Deployment — Choose Your Workspace Model
Data stays under your control. Deploy locally or within your environment — with privacy and compliance built into the architecture. Trust & security.
Private Workspace (Local Mode)
Run the workspace entirely on your device. No login, no data transfer — full control for private use and evaluation.
- Data stays on your device
- No account or backend required
- Instant, standalone deployment
Managed Workspace (Client Environment)
Deploy within your organization's environment with persistent data, collaboration, and audit-ready capabilities.
- Backend-enabled and organization-aware
- Persistent records and audit evidence
- Built for teams and operational workflows
See Pricing